Elias looked at his desk. There, sitting next to his keyboard, was a small, ornate brass key he had found in his mail that morning. He had spent all day wondering what it opened.
Suddenly, the clock on his computer screen flickered. 11:58 PM. 11:59 PM.
He played the audio. It was his own voice, sounding exhausted. File: Once.Again.zip ...
“It’s April 28th,” the recording said. “I’m leaving this in the zip folder because the cloud keeps syncing the old versions. If you’ve found this, don’t look for the key. The key is what triggers the reset. Just let the clock run out.”
His heart hammered. He reached for the key, intent on throwing it out the window, but as his fingers brushed the cold metal, the screen went black. A white prompt appeared in the center of the darkness: Elias looked at his desk
When he unzipped it, there were no photos or documents—only a single text file and an audio clip. He clicked the text file first. It was a log of dates, all exactly twenty-four hours apart, stretching back three years. At the bottom, a single line: “If you are reading this, the cycle failed. Try again.”
Elias found the file on an old drive he didn’t recognize. It was simply titled Once.Again.zip . Suddenly, the clock on his computer screen flickered
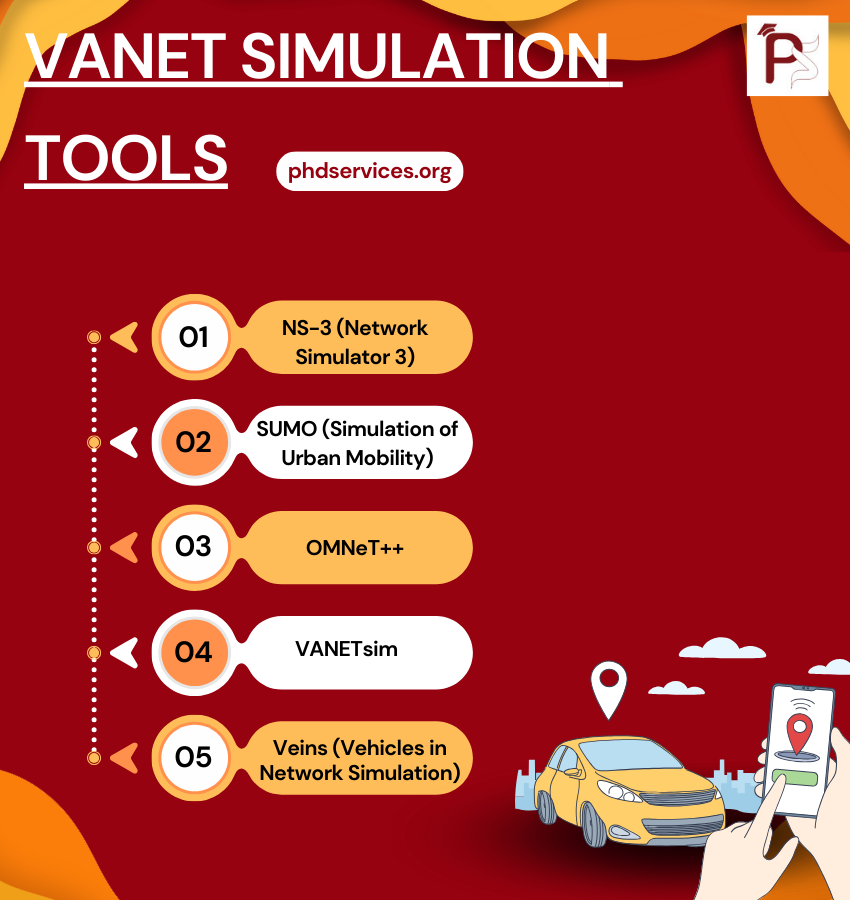
VANET Simulation Tools Topics & Ideas
We utilize cutting-edge VANET Simulation Tools according to your proposed concept. Explore the various Topics & Ideas that are being explored by phdswervices.org. It is common for research students to make mistakes in certain areas, and that is why we offer the guidance of our writers. We ensure that your topic is properly framed with appropriate keywords to enhance its effectiveness.
- Road traffic and geography topology based opportunistic routing for VANETs
- Cooperative pseudonym change scheme based on the number of neighbors in VANETs
- Boosting named data networking for data dissemination in urban VANET scenarios
- VANET Based Vehicle Tracking Module for Safe and Efficient Road Transportation System
- Design and performance evaluation of a PMIPv6 solution for geonetworking-based VANETs
- SEGM: A secure group management framework in integrated VANET-cellular networks
- Secure and privacy-aware traffic information as a service in VANET-based clouds
- A cross layer approach for efficient multimedia data dissemination in VANETs
- Reliability and energy-efficiency analysis of safety message broadcast in VANETs
- Asking neighbors a favor: Cooperative video retrieval using cellular networks in VANETs
- Intelligent Adjustment Forwarding: A compromise between end-to-end and hop-by-hop transmissions in VANET environments
- Performance analysis and implementation of proposed mechanism for detection and prevention of security attacks in routing protocols of vehicular ad-hoc network (VANET)
- A lightweight authentication and privacy-preserving scheme for VANETs using TESLA and Bloom Filters
- LIAP: A local identity-based anonymous message authentication protocol in VANETs
- Practical secure and privacy-preserving scheme for value-added applications in VANETs
- The insights of message delivery delay in VANETs with a bidirectional traffic model
- Nexthop selection mechanism for nodes with heterogeneous transmission range in VANETs
- QualityScan scheme for load balancing efficiency in vehicular ad hoc networks (VANETs)
- A mobility-based scheme for dynamic clustering in vehicular ad-hoc networks (VANETs)
- Regression based critical information aggregation and dissemination in VANETs: A cognitive agent approach