Hiphop Tamizha's "Kadaisi Ulaga Por" (The Last World War), released in 2024, transcends the typical action-packed sci-fi war movie genre. It embeds a...
Silently stealing data without triggering alarms.
Crafting payloads that bypass basic email filters.
The name can be off-putting or unprofessional if you plan to read it in an office or on a plane.
You need a foundational understanding of networking (IPs, ports, CMD/Terminal) to follow along effectively. 🛠️ Key Topics Covered
Like all tech books, specific versions of software (Metasploit, Kali tools) may have changed since publication.
Silently stealing data without triggering alarms.
Crafting payloads that bypass basic email filters.
The name can be off-putting or unprofessional if you plan to read it in an office or on a plane.
You need a foundational understanding of networking (IPs, ports, CMD/Terminal) to follow along effectively. 🛠️ Key Topics Covered
Like all tech books, specific versions of software (Metasploit, Kali tools) may have changed since publication.
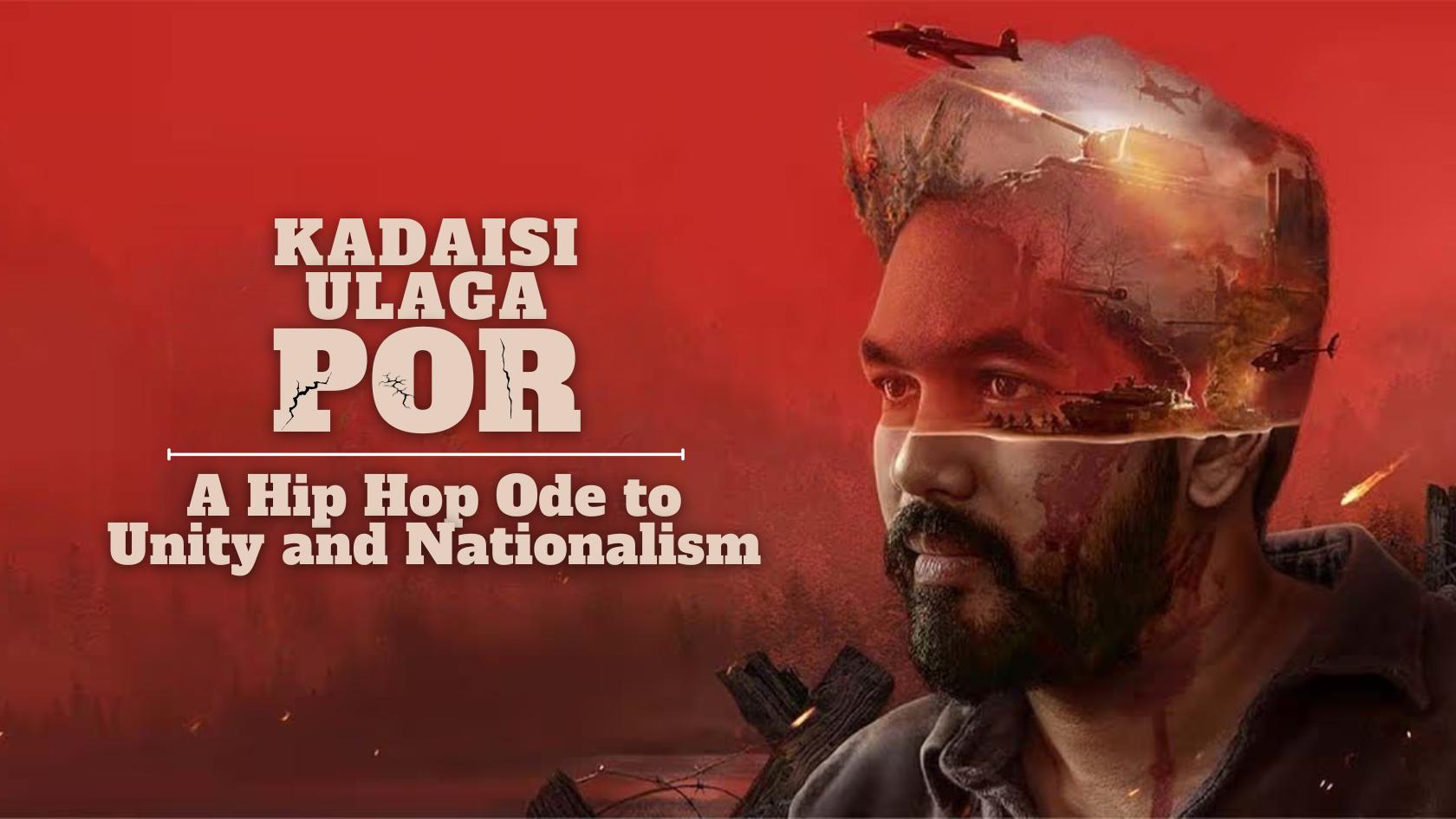
Hiphop Tamizha's "Kadaisi Ulaga Por" (The Last World War), released in 2024, transcends the typical action-packed sci-fi war movie genre. It embeds a...
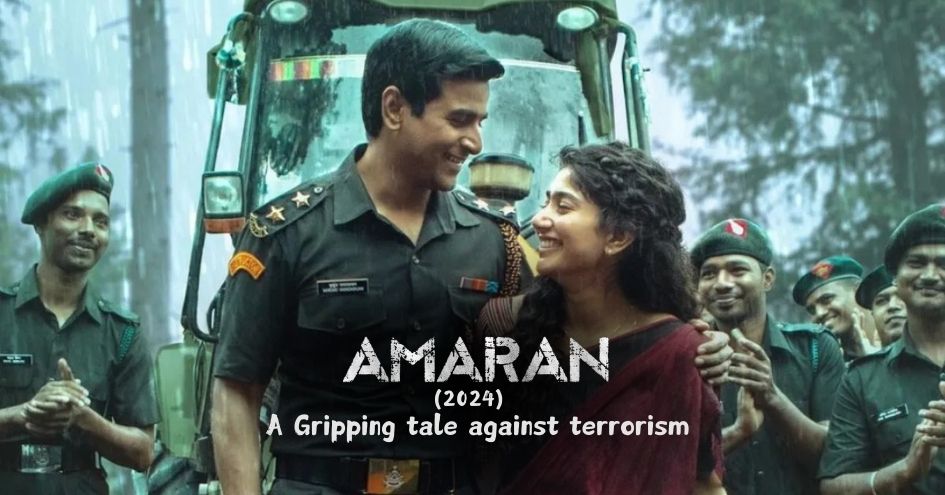
Creating war films is a challenging endeavor, and capturing the emotional struggles of soldiers and their families adds an even greater layer of com... How To Hack Like a Pornstar: A Step By Step Pro...
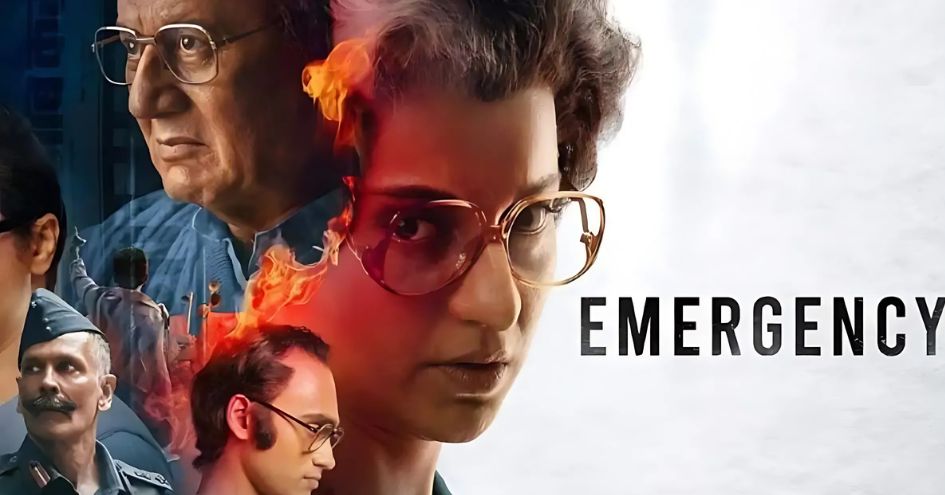
Emergency, directed by Kangana Ranaut, is a bold and gripping political drama that delves into one of Independent India’s darkest periods: the Emergen... Silently stealing data without triggering alarms